Another cyber attack, called Petya, was wreaking havoc on computer systems from Ukraine to the United State, grinding business to a halt at some of the world’s largest companies.
Law enforcement still hasn’t found a kill switch for this latest ransomware virus, called Petya, that demands users to pay a fee to get their files back, but experts say the attack could have been prevented.
But how? To find out, Metro talked to two cybersecurity experts: Jack Danahy, CTO of Barkly and Konrad Martin of Tech Advisors.
What is the Petya cyberattack?
Remember the ransomware attack that took down the National Health Service in Great Britain in May? It was called WannaCry and Petya is basically WannaCry 2.0.
“Petya is very similar ransomware that comes up with warning encrypts data and asks for a ransom in Bitcoin,” Martin said. Bitcoin is an online currency that can be bought and sold anonymously.
Petya uses Eternal Blue, the same security vulnerability exploited by WannaCry hackers, but instead of just encrypting files, this new cyber attack also encrypts the hard drive’s master boot record. Instead of making individual files inaccessible, this actually makes the entire system nonfunctional until the ransom is paid.
“This is a new advancement in order make it more likely victims will pay the ransom,” Danahy said.
Hackers are demanding $300 worth of Bitcoin, which is equivalent to about one-tenth of a Bitcoin.
Who did the Petya cyber attack target and why?
The exact size and scope of the attack are still be determined, but what authorities do know is that the virus first took hold Tuesday in Ukraine, where it festered and by Wednesday it was attacking computer systems the world over.
Businesses and industries across the U.S., in the U.K., France, Germany, Denmark, India, Australia and New Zealand were feeling the effects of the virus by Wednesday, CNN reported.
The hackers had even targeted Mondelez, the U.S.-based snack company that owns Oreos and Cadbury chocolate.
But Danahy warned just because it’s the big companies grabbing the headlines, doesn’t mean small- and medium-sized businesses weren’t victimized as well.
“A lot of these [cyberattcks] are random. They target a range of random IP addresses or email addresses,” he said. “We have seen a lot of people in much smaller organizations — police deptartments, physicians offices — get whacked.”
Was Petya preventable?
Simply put: Yes. It’s happened before.
Petya exploited the same vulnerability in a Microsoft security network that WannaCry benefitted from.
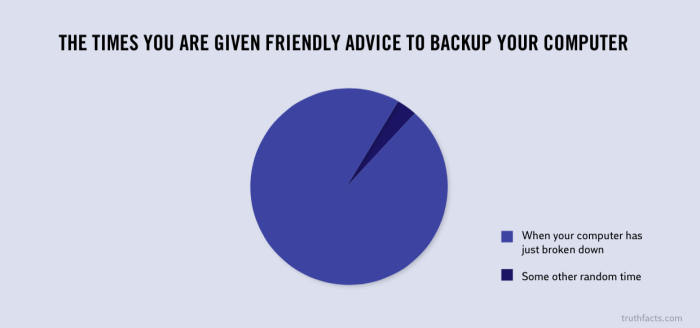
Microsoft actually released what’s called a “patch” to fix the vulnerability back in March and computer systems that hadn’t updated fell vulnerable to attacks. Ditto for Petya.
“Either enough people didn’t get the message or they had other business priorities, but it just shows you should really do better patching to discourage attacks,” Danahy said.
Both attacks also targeted end-user vulnerabilities — individual computer users who click on popups or email links that contain malware.
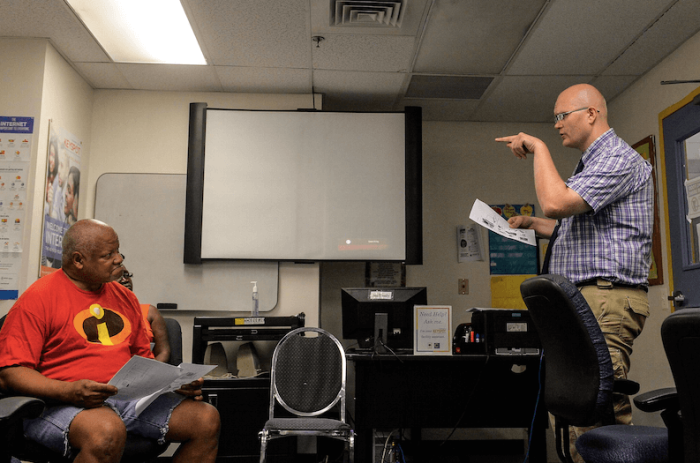
“Ninety-nine percent of the time the biggest security threat you have are your employees. It comes down to human vulnerability and a lack of education,” Martin said.
Danahy recommended three steps companies should take to protect themselves from cyberattacks: understand the services your running and that there is software behind it, keep the software up to date and educate endpoint users to make sure they understand opening things and clicking things can be a problem.
“I think if companies spent a little time thinking about those three things, we’ll be in a much better place,” he said.